How Virtualization Transforms Disaster Recovery Plans?

Virtualization plays a crucial role in enhancing data disaster recovery strategies for organizations. Here are the key ways in which virtualization contributes to effective disaster recovery:
Improved Backup and Recovery
- Snapshots: Virtual machines (VMs) can be easily backed up using snapshots, which capture the entire state of the VM at a specific point in time. This allows for quick restoration, minimizing downtime.
- Rapid Recovery: In the event of a disaster, entire systems can be restored in minutes rather than hours or days, significantly reducing Recovery Time Objectives (RTO).
Hardware Independence
- Flexibility: Virtualization abstracts the hardware layer, allowing VMs to run on different physical machines. This is particularly beneficial when the original hardware is unavailable due to a disaster.
- Resource Allocation: Resources can be dynamically allocated to VMs based on current needs, ensuring that critical systems receive the necessary computing power during recovery.
Cost Efficiency
- Reduced Infrastructure Costs: Traditional disaster recovery often requires maintaining duplicate hardware, which can be expensive. Virtualization reduces the need for physical infrastructure, leading to significant cost savings.
- Disaster Recovery as a Service (DRaaS): Organizations can leverage cloud-based DRaaS solutions, which allow them to replicate and back up systems in the cloud, further reducing costs associated with physical disaster recovery sites.
Testing and Validation
- Non-Disruptive Testing: Virtualization allows organizations to create isolated test environments to simulate disasters and validate their recovery plans without affecting live operations. Regular testing ensures that recovery procedures are effective and up-to-date.
- Confidence in Recovery Plans: By regularly testing disaster recovery plans, organizations can identify potential issues and fine-tune their strategies, improving overall confidence in their disaster recovery capabilities.
Enhanced Recovery Point Objectives (RPO)
- Frequent Backups: Virtualization enables more frequent and efficient data backups, helping organizations achieve lower RPOs. Techniques like incremental backups and continuous data protection (CDP) minimize data loss.
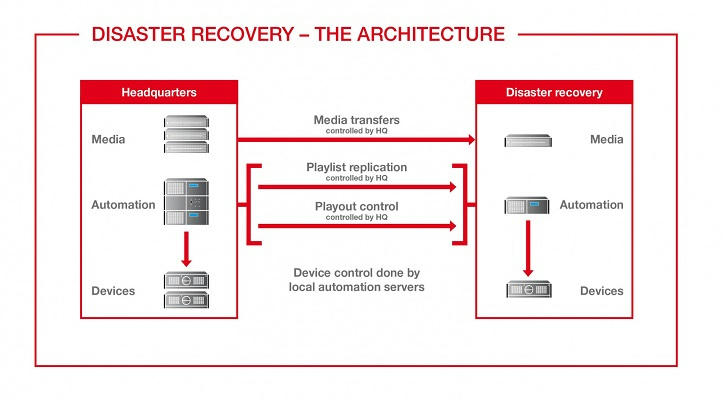
- Real-Time Data Replication: Organizations can replicate data and applications in real-time or at scheduled intervals to a disaster recovery site, ensuring continuous data availability.
Scalability and Flexibility
- Adaptable Solutions: Virtualization allows businesses to scale their disaster recovery solutions according to their needs, making it easier to adjust to changing business requirements.
- Geographic Redundancy: Organizations can store backups in multiple locations, reducing the risk of data loss due to localized disasters.
Enhanced Recovery Point Objectives (RPO)
- Simplified Administration: Centralized management consoles enable administrators to monitor and manage VMs, storage, and network resources from a single interface, streamlining disaster recovery efforts.
Best Practices for Implementing Virtualization in Disaster Recovery
- Conduct a Risk Assessment: Identify critical systems and evaluate potential risks.
- Develop a Comprehensive DR Plan: Outline backup schedules, recovery procedures, and roles.
- Choose the Right Tools: Invest in robust virtualization and disaster recovery solutions.
- Regularly Test and Update: Ensure the DR plan remains effective through regular testing.
- Train Your IT Team: Provide training on best practices and tools for disaster recovery.
By following these practices, organizations can effectively implement virtualization in their disaster recovery strategies, ensuring resilience and continuity in the face of disruptions.
Strategies for Encryption and Authentication
Encryption and authentication are critical components of a robust security strategy. They help protect sensitive data and ensure that only authorized users can access systems and information. Here are some key strategies to consider:
1. Implement Strong Encryption Standards
- Use Industry-Standard Algorithms: Adopt widely accepted encryption algorithms such as AES (Advanced Encryption Standard) with a key length of at least 256 bits for data at rest and in transit.
- Regularly Update Encryption Protocols: Stay informed about the latest developments in encryption technology and update protocols as necessary to protect against vulnerabilities.
2. Encrypt Data at Rest and in Transit
- Data at Rest: Ensure that sensitive data stored on servers, databases, and storage devices is encrypted to protect it from unauthorized access.
- Data in Transit: Use protocols like TLS (Transport Layer Security) to encrypt data transmitted over networks, safeguarding it from interception during transmission.
3. Implement Multi-Factor Authentication (MFA)
- Add Layers of Security: Require users to provide two or more verification factors to gain access to systems, such as a password combined with a one-time code sent to their mobile device.
- Adapt to User Behavior: Consider implementing adaptive authentication that adjusts security measures based on user behavior and risk levels.
4. Regularly Review and Update Access Controls
- Role-Based Access Control (RBAC): Implement RBAC to ensure that users have access only to the information necessary for their roles, minimizing the risk of unauthorized access.
- Periodic Access Reviews: Conduct regular audits of user access rights to ensure that permissions are up-to-date and revoke access for users who no longer require it.
5. Monitor and Audit Authentication Logs
- Log Access Attempts: Maintain detailed logs of authentication attempts, including successful and failed logins, to identify potential security incidents.
- Regular Audits: Conduct periodic audits of authentication logs to detect unusual patterns or unauthorized access attempts.
Implementing effective encryption and authentication strategies is essential for protecting sensitive data and ensuring secure access to systems. By adopting these strategies, organizations can significantly reduce the risk of data breaches and enhance their overall security posture.
Conclusion
Virtualization has transformed disaster recovery by providing organizations with a flexible, efficient, and cost-effective way to protect their critical data and systems. By leveraging virtualization technologies, businesses can ensure quick recovery from disasters, maintain business continuity, and safeguard their digital assets against unexpected events.